Newly unsealed grand jury documents reveal that two Sudanese nationals allegedly attempted to launch thousands of distributed denial of service (DDoS) attacks against systems around the world. The documents allege that these hacks were intended to cause significant economic and technological harm to government agencies and businesses, and in some cases even physical damage.
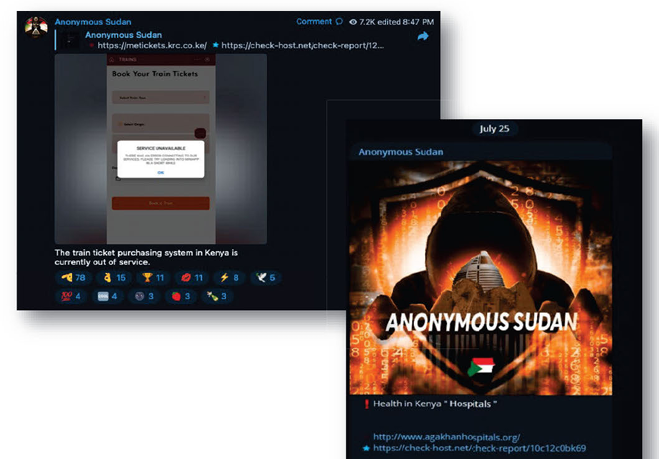
The U.S. Department of Justice (Department of Justice) announced the indictment against Ahmed Salah Yusif Omer and Alaa Salah Yusuf Omer, which was presented to a federal grand jury. The two, as part of the cybercriminal group Anonymous Sudan and a commercial cyberattack service, were allegedly involved in more than 35,000 DDoS attacks against hundreds of organizations, websites and networks as part of a “hacktivism” scheme. There is.
Despite Anonymous Sudan’s claims to be an activist group, the pair also held the systems of some companies and organizations to ransom for fees as high as $1,700 per month.
Both men are charged for their roles in a coordinated cyber attack, including one count each of conspiracy to harm protected computers. According to court records filed last June in the U.S. Central District Court of California, Ahmed faces three additional charges for damaging a protected computer and faces the statutory maximum life sentence in federal prison. There is a possibility that he will be sentenced.
The brothers’ activities date back to early 2023. According to a statement from the Department of Justice, the two used a distributed cloud attack tool (DCAT) called the Skynet botnet to “conduct devastating DDoS attacks and publicly claim credit for them.” Ahmed posted a message on Anonymous Sudan’s Telegram channel, saying, “The United States must prepare. It will be a very large attack. Just like we did in Israel, we will It will be done in the United States “soon”, he said.
One of the indictments lists 145 “overt acts” against organizations and entities in the United States, the European Union, Israel, Sudan, and the United Arab Emirates (UAE). Skynet botnet attacks attempted to disrupt services and networks at airports, software networks, companies including Cloudflare, X, Paypal, and Microsoft, and crippled Outlook and OneDrive last June. The attacks targeted state and federal government agencies and websites, including the Federal Bureau of Investigation (FBI), Department of Defense, and Department of Justice, as well as hospitals, including a major attack on Cedars-Sinai Hospital in Los Angeles. As a patient, this caused a stagnation in medical services. Transferred to another hospital. The hospital attack led to hacking charges against Ahmed, which could result in a life sentence.
“It’s still there after more than three hours,” Ahmed wrote on Telegram in February. “They are desperately trying to repair it, but in vain. They bombed our hospital in Gaza and killed me. We have closed your hospital too. An eye for an eye…”
FBI special agents sold access to the Skynet botnet to more than 100 customers to carry out attacks against various victims who worked with law enforcement agencies including Cloudflare, Crowdstrike, Digital Ocean, Google, and PayPal. We collected evidence of the illegal activities of the two, including logs showing what they had done.
Amazon Web Services (AWS) was one of Anonymous Sudan’s victims as part of a hack-for-hire scheme, according to court documents and an AWS statement. The AWS security team worked with FBI cybercrime investigators. The security team discovered that the attack “came from a set of cloud-based servers, many of which were hosted on server hosting providers in the United States.” This discovery allowed the FBI to determine that the Skynet botnet attack came from DCAT, rather than a botnet that forwards DDoS to victims via cloud-based servers and open proxy resolvers. .
Perhaps the group’s most brazen and dangerous attack took place in April 2023, targeting an Israeli rocket warning system called Red Alert. The mobile app provides real-time updates on missile attacks and security threats. The DDoS attack attempted to penetrate some of Red Alert’s internet domains. Ahmed claimed responsibility for the Red Alert attack on Telegram and similar DDoS attacks on Israeli power companies and the news website Jerusalem Post.
“This group’s attacks were callous and brazen, with the defendants attacking hospitals that provide emergency care to patients,” U.S. Attorney Martin Estrada said in a statement. “My office is committed to protecting our nation’s infrastructure and the people who use it, and we will hold cybercriminals accountable for the serious harm they cause.”